As the digital realm continues to expand, web applications have become an integral part of our daily lives. However, their ubiquity has also exposed them to a multitude of security risks, thus making it imperative to ensure the protection of user data and sensitive resources. At the heart of this protection lies effective identity management testing, a crucial component of web application security. This article embarks on an in-depth journey through the realm of web app identity management testing, elucidating its significance, methodologies, and best practices.
Demystifying Web App Identity Management
Web application identity management encompasses the intricate processes, tools, and strategies that underpin the authentication, authorization, and user management aspects of an application. In essence, it ensures that the right individuals have the appropriate access privileges to specific resources within the application. Next, as an indispensable facet of overall web app security, robust identity management serves as a bulwark against unauthorized access, data breaches, and compromised user accounts.
Significance of Identity Management Testing
The pivotal role of identity management testing stems from its role in verifying and fortifying the security measures within a web application. Its significance is multifaceted, contributing to:
- Mitigating Unauthorized Access: Identity management testing acts as a gatekeeper, allowing only authenticated and authorized users to access sensitive resources. This preventive measure substantially reduces the risk of unauthorized breaches and data compromise.
- Counteracting Insider Threats: Through meticulous evaluation of user access permissions, identity management testing identifies potential insider threats posed by malicious or negligent employees, enabling preemptive actions to be taken.
- Preserving Data Integrity: Proper identity management testing ensures that user roles, permissions, and data interactions are meticulously defined and executed, safeguarding the integrity of valuable information.
- Nurturing Regulatory Compliance: Many industries are subject to stringent regulations governing data protection and access control. Identity management testing facilitates adherence to these regulations, ensuring that user data is handled with due diligence.
Methodologies for Identity Management Testing
Authentication Testing:
- Strength Evaluation: Rigorously assess the potency of authentication mechanisms such as password policies, multi-factor authentication (MFA), and single sign-on (SSO).
- Vulnerability Analysis: Test for prevalent vulnerabilities like credential stuffing, brute force attacks, and session hijacking to fortify authentication processes.
Authorization Testing:
- Access Control Scrutiny: Thoroughly examine role-based access control (RBAC) and permissions to guarantee precise user access.
- Privilege Escalation Examination: Uncover horizontal and vertical privilege escalation vulnerabilities, rectifying any access control discrepancies.
- Consistency Verification: Ensure consistent enforcement of access controls across all application components to prevent potential security gaps.
Session Management Testing:
- Session Timeout Evaluation: Scrutinize session timeout mechanisms to avert unauthorized access via session fixation or hijacking.
- Session Termination Assurance: Verify that sessions terminate accurately upon logout or prolonged inactivity, thwarting unauthorized access attempts.
Federation and Single Sign-On Testing:
- External Integration Assessment: Test the integration of external identity providers for SSO and federation to identify potential security loopholes.
- Token Security Validation: Rigorously validate the security of token exchange and user attribute sharing between identity providers and the application to thwart token-based attacks.
Account Management Testing:
- Robustness of Processes: Evaluate the robustness of account registration and password recovery processes to guard against vulnerabilities.
- Secure Password Reset: Ensure that password reset links are secure and expiration policies are judiciously implemented to prevent unauthorized access.
Best Practices for Effective Identity Management Testing
- Holistic Risk Assessment: Prioritize testing efforts based on a meticulous assessment of potential vulnerabilities and their potential impact.
- Realistic Test Scenarios: Craft test cases that simulate real-world scenarios, including a diverse range of user roles and access levels, to comprehensively evaluate the system.
- Input Validation Vigilance: Enforce stringent input validation checks for user authentication, authorization, and session management to preempt injection attacks.
- Multi-Factor Authentication (MFA) Implementation: Advocate for the integration of MFA to bolster the security of authentication processes.
- Championing Least Privilege: Adhere to the principle of least privilege, ensuring that users are endowed with minimal access necessary to perform their designated tasks.
- Ongoing Auditing and Monitoring: Institute continuous monitoring and periodic audits of identity management processes to promptly detect and rectify vulnerabilities.
- Configurations Tailored for Security: Modify default configurations for authentication and authorization mechanisms to enhance security and resilience.
- Resilient Token Management: Establish secure mechanisms for token storage, transmission, and validation to stymie token-based attacks.
Conclusion
In an increasingly interconnected digital landscape, web application identity management testing assumes a paramount role in safeguarding sensitive user data and resources. Consequently, by rigorously scrutinizing authentication, authorization, session management, and related processes, organizations can effectively identify vulnerabilities and implement robust security measures. Furthermore, as the technological landscape continues to evolve, continual identity management testing will be pivotal in thwarting emerging threats and upholding the sanctity of user data. With that being said, by embracing the best practices delineated in this article, organizations can forge a path toward creating more secure and resilient web applications, thus fortifying their digital presence in a world driven by connectivity and innovation.
For more information about agile testing, check out more videos from the AgileTest Academy series
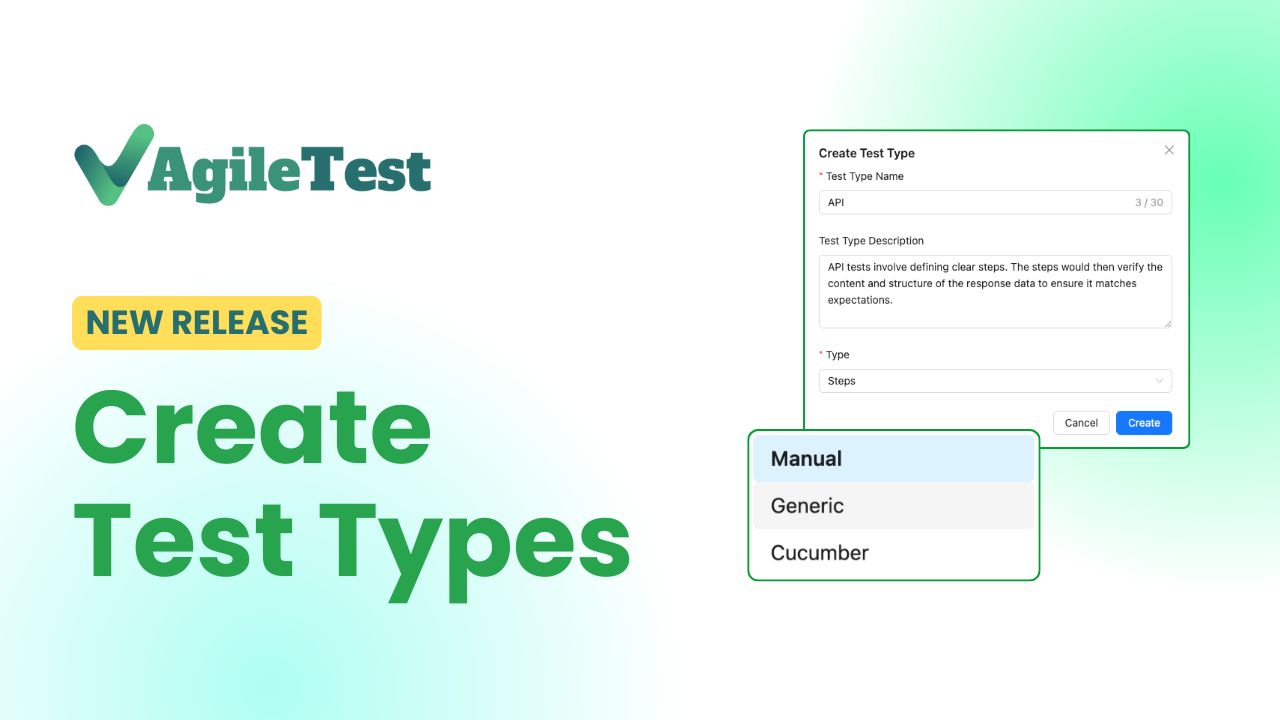
If you love the testing experiences, try our app on the Atlassian Marketplace!